LARK KMS (Key Management System)
LARK KMS serves as the foundation of secure and intelligent key management, ensuring the generation, distribution, and lifecycle control of cryptographic keys with uncompromising security and efficiency. From seamless remote
key injection to real-time monitoring and automated key rotation,
it empowers industries like finance, payment processing,
and enterprise security to operate with enhanced protection,
compliance, and reliability.
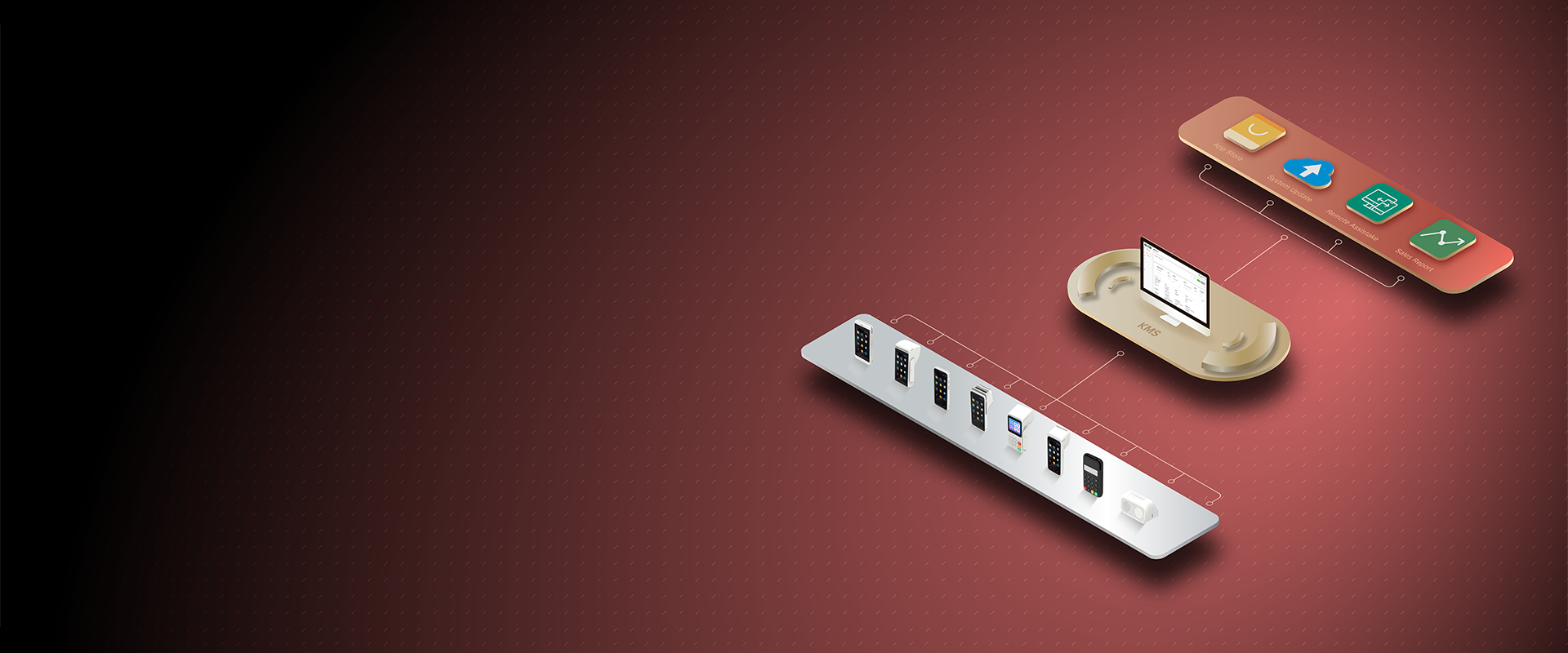
What is LARK KMS?
LARK KMS is a comprehensive Key Management System (KMS) that streamlines the entire lifecycle of cryptographic keys—from generation and distribution to rotation and revocation. Designed for industries like finance, payment processing, and enterprise security, it goes beyond traditional key management to deliver enhanced security, automation, and seamless control.
Key Features
Secure Key Generation & Storage
Supports MKSK (Master Key/Sub Key) and DUKPT (Derived Unique Key Per Transaction) encryption structures.
All cryptographic operations, including key generation, encryption, and signing, are performed securely within HSM.
Multi-layer authentication and access control to prevent unauthorized key access.
Automated Key Lifecycle Management
Batch key provisioning for large-scale deployments.
Supports scheduled key updates and automatic key rotation to enhance security.
Task-based key injection and expiration tracking ensure complete control.
Remote Key Distribution
Offers tiered management for organizational hierarchies, supporting branches and subsidiaries. Ensures secure operations with role-based access control and multi-tenant architecture.
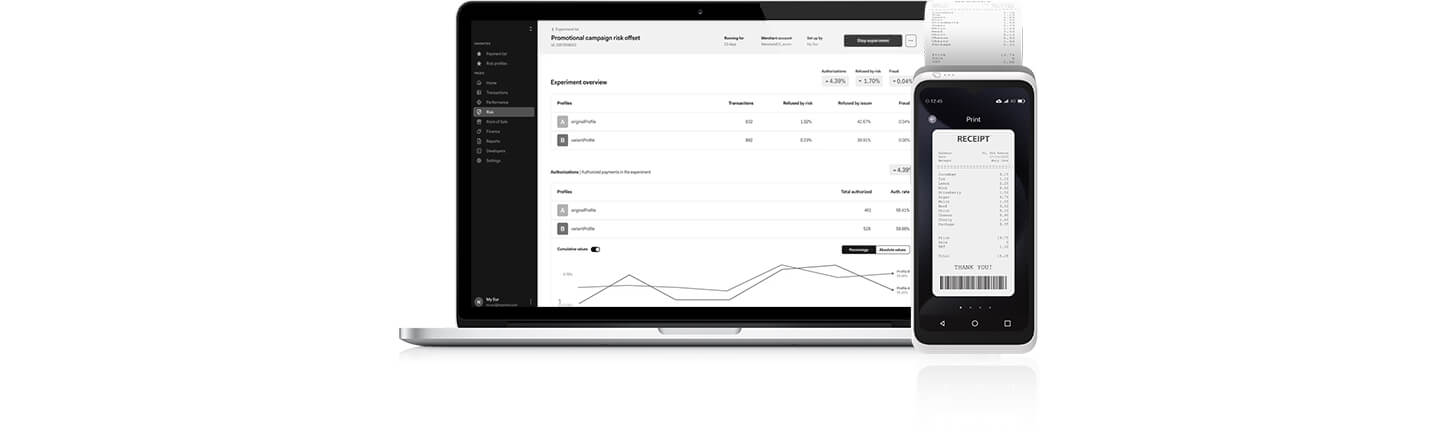
Real-Time Monitoring & Analytics
Live tracking of key injection status, updates, and lifecycle management.
Detailed audit logs help businesses meet regulatory compliance requirements.
Automated security alerts and anomaly detection for proactive risk mitigation.
Seamless Integration with Third-Party Systems
Open APIs and SDKs enable seamless integration with payment gateways, banking networks, and enterprise security infrastructures.
Multi-tenant key management allows businesses to set security policies for multiple branches and subsidiaries.
Dive Deeper
Discover What Sets Us Apart
Advanced Key Ecosystem
Comprehensive and Scalable Key Management
Supports multiple key management frameworks for different business needs.
Centralized repository for efficient deployment and security.
Automated key rotation and backup to ensure uninterrupted security.
Intelligent Security & Oversight
Real-Time Key Monitoring and Compliance Enforcement
Track key usage, status, and security policies in real-time.
Perform remote key revocations and replacements when needed.
Group terminals and manage access levels for enhanced security.
Efficient Key Deployment & Updates
Automated Scheduling & Secure Distribution
Seamless remote key injection across devices and locations.
Scheduled updates and key replacements with zero downtime.
Automated distribution process minimizes manual intervention.

Proactive Security & Troubleshooting
Advanced Security and Remote Issue Resolution
Remote diagnostics and troubleshooting to resolve key-related issues.
Encryption validation and compliance monitoring for maximum protection.
Detailed security reports and alerts for proactive threat management.

Data-Driven Decision Support
Comprehensive Analytics and Reporting
Generate detailed reports on key usage, security events, and compliance tracking.
Identify trends in key lifecycle management for optimized security.
Automated audit trails to ensure compliance with regulatory standards.

Secure Access Management
Multi-Layer Access Control & Notifications
Role-based authentication ensures that only authorized personnel can access the system.
Multi-tenant architecture supports different security policies across locations.
Automated notifications for key expirations, anomalies, and updates.
Get Started with LARK KMS in Five Steps
Reach Out
Contact us to begin your secure key management journey.
Assess Needs
Collaborate with our team to evaluate your business security requirements and encryption needs.
Tailor Solution
Receive a customized LARK KMS deployment strategy designed to fit your operational and security framework.
Seamless Deployment
Deploy and configure LARK KMS effortlessly, integrating HSM-based encryption and automated key management into your existing infrastructure.
Go Live
Launch your fully secured key management system and start optimizing operations with real-time monitoring, automated updates, and compliance tracking.

